OPERATION EPIC FURY: THE CYBER WAR THAT FOLLOWED THE MISSILES

Situation Report
- 150+ Hacktivist incidents in first 72 hrs post-strikes
- 110 Organizations hit across 16 countries, Feb 28 – Mar 2
- ~4% Iran's internet connectivity remaining post-offensive
What Happened: The 10-Day Cyber Escalation Timeline
The Middle East conflict entered a defining new phase on February 28, 2026, when the United States and Israel launched a synchronized hybrid offensive — codenamed Operation Epic Fury (U.S.) and Operation Roaring Lion (Israel) — targeting Iranian military, leadership, and nuclear-linked sites. Within hours, the cyber domain erupted in parallel with the kinetic strikes, creating spillover risks now reaching private sector organizations globally.
What followed was not a conventional cyberattack wave. It was a multi-domain hybrid campaign combining state-sponsored offensive operations, a 70+ group hacktivist surge, AI-enhanced phishing campaigns, physical destruction of commercial cloud infrastructure, and Iran's near-total internet blackout — all compressed into a single week.
⚡ Eclipse Intel Assessment
"The events of late February and early March 2026 compressed what analysts had warned were plausible worst-case scenarios into a single week. A major cloud provider's physical infrastructure has been damaged by military action. A nation's internet has been functionally erased. State-sponsored and hacktivist operations are running in parallel with kinetic strikes on a scale not previously documented."
Timeline:
18 February 2026: UAE Intercepts Up to 200,000 Attacks Per Day
UAE authorities disclosed interception of between 90,000 and 200,000 cyberattacks per day, with over 70% linked to state-sponsored threat actors. On February 21, the UAE Cybersecurity Council announced disruption of coordinated attacks described as "terrorist in nature," involving ransomware deployment, network infiltration, and phishing campaigns targeting national platforms — a sign of the pre-positioning already underway before the Feb 28 strikes.
28 February 2026: Operations Epic Fury & Roaring Lion — The Opening Salvo
Joint U.S.-Israeli strikes on Iran triggered a sweeping parallel cyber operation that disrupted Iran's digital infrastructure, with internet connectivity dropping to approximately 1–4% of normal levels. Within hours, hacktivist faction the 313 Team publicly declared targeting of Israel, Jordan, the U.S., Saudi Arabia, UAE, and Kuwait. The first DDoS attack of this wave was launched by Hider Nex (Tunisian Maskers Cyber Force). Seventy-plus hacktivist groups mobilized across Telegram channels over the following 24 hours.
28 Feb – 2 March 2026: 150+ Incidents — Banks, Airports, Telecoms Targeted
Over 150 hacktivist incidents recorded across open channels within 72 hours, hitting 110 organizations in 16 countries. Ten financial institutions were targeted in coordinated disruption attempts, including major banks in Saudi Arabia, Jordan, and Israel. DieNet claimed DDoS attacks on airports in Bahrain, Sharjah, and the UAE. Seven aviation and logistics entities, multiple government ministries, and telecoms providers were also targeted. UAE phone and online banking services experienced disruption, though most claims were not independently verified as deep system breaches.
1 March 2026: AWS UAE Data Centre Struck — Cloud Goes Kinetic
Amazon Web Services confirmed that unidentified objects struck at least one data centre in its Middle East UAE Region (ME-CENTRAL-1), causing a fire and localized power loss. Secondary disruption was reported in the Bahrain region (ME-SOUTH-1). This is the first publicly confirmed instance of kinetic military action causing commercial cloud service outages at this scale — a landmark moment for private sector risk assessment, particularly for organizations with single-region deployments in the Middle East.
1 March 2026: Fake RedAlert APK — Mobile Surveillance Campaign Detected
Unit 42 analysts observed a malicious Android APK designed to mimic Israel's official missile alert application (RedAlert) being distributed via Hebrew-language SMS links. Once installed, the malware silently harvested contacts, SMS logs, IMEI numbers, and email credentials using encrypted exfiltration mechanisms. By leveraging genuine wartime anxiety about incoming missile alerts, adversaries achieved a high installation rate — a model Eclipse Intel expects to be replicated in other formats targeting civilians and corporate staff in the region.
3–8 March 2026: Retaliation Phase — Missiles, Drones & Sustained Cyber Operations
From March 1 onward, waves of Iranian ballistic missiles and drones targeted Israel, GCC states, and U.S. military bases, confirming Tehran's retaliation would not be limited to symbolic posturing. In the cyber domain, HydraC2 botnet calls to action were observed, ransomware group Sicarii activated, and Handala escalated to issuing direct physical death threats to Iranian diaspora critics — leaking home addresses to claimed physical operatives.
Eclipse Intel assesses the retaliation phase is ongoing with no near-term de-escalation signal.
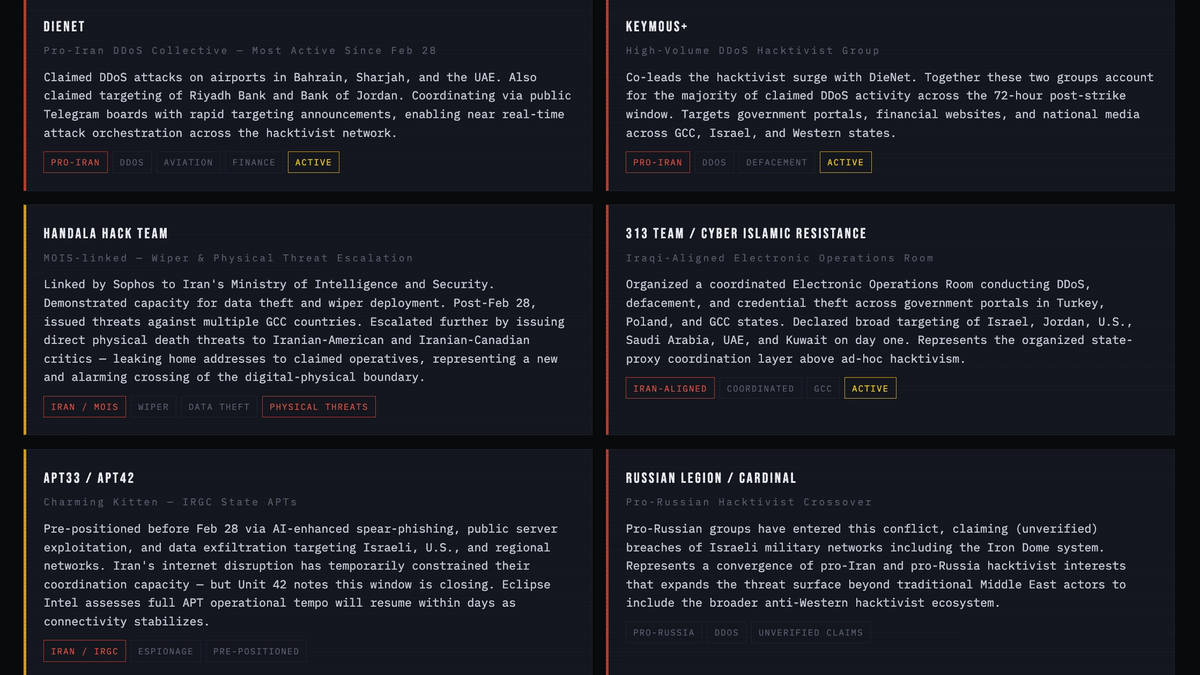
Active Threat Actors
Who Is Behind the Attacks: 2026 Threat Actor Landscape
Eclipse Intel is tracking activity from over 70 groups activated since February 28. Keymous+ and DieNet alone drove nearly 70% of all hacktivist DDoS activity in the first four days, per Radware. Below are the key actors your security team must understand.
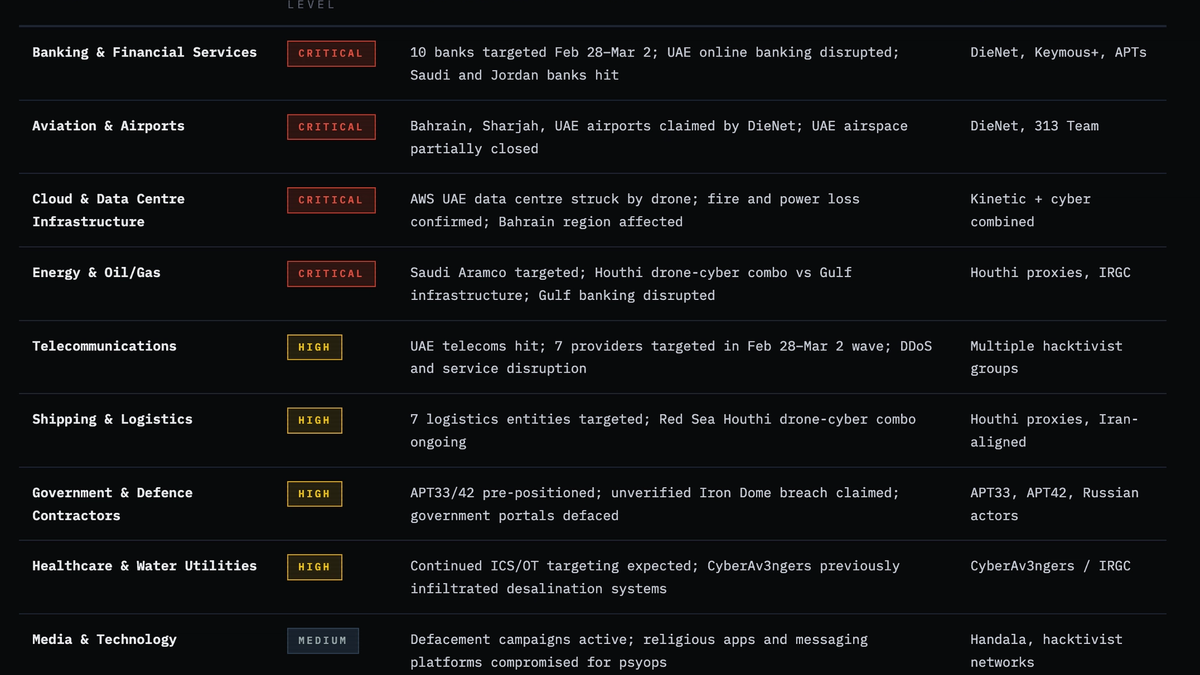
Sector Risk Assessment
Which Private Sector Industries Face the Greatest Exposure
Based on confirmed and claimed incidents from Feb 26 – Mar 8, 2026. Organizations in Israel, the U.S., and allied nations face direct or indirect targeting across these sectors. During periods of instability, operations intensify and target critical infrastructure, energy, government, and private industry far beyond the immediate conflict zone.
⚡ Eclipse Intel Assessment
Private sector directly involved in aiding to the Military can be targeted as well.
New 2026 Attack Vectors
What's Different and More Dangerous in This Cycle
AI-Enhanced Phishing & Ransomware at Scale
Multiple security firms have documented the use of generative AI to improve phishing realism, scale fraud campaigns, and enhance ransomware social engineering. AI-generated lures now convincingly mimic legitimate business correspondence, invoice requests, and wartime government communications in multiple languages. Standard email filtering is increasingly inadequate against this generation of campaigns.
Kinetic-Cyber Convergence: Cloud Is Now a Target
The drone strike on the AWS UAE data centre is a watershed moment for enterprise risk. Physical military action is now directly disrupting commercial cloud services. Organizations relying on single-region Middle East deployments face compounded risk: simultaneous cyber and kinetic disruption to the same infrastructure. Multi-region redundancy is no longer optional — it is a survival requirement for organizations with regional exposure.
Ransomware as State-Directed Retaliation
Former FBI Cyber Division Deputy Assistant Director Cynthia Kaiser stated publicly: "Iran will likely respond in cyberspace. It will probably look like cybercrime and ransomware." Eclipse Intel advises treating any ransomware incident in the next 30–60 days — particularly in sectors targeted in this advisory — as a potential state-directed operation using financially-motivated actors as deniable proxies. Standard criminal ransomware playbooks are insufficient response protocols.
Digital-to-Physical Threat Escalation
Handala's decision to leak home addresses of diaspora critics to claimed physical operatives marks a dangerous new escalation in the digital-physical threat boundary. Organizations with Iranian-American, Iranian-Canadian, or Iranian-European staff must be aware that threat actors are now willing to leverage cyber-gathered intelligence to enable physical harm. Personal data security for at-risk employees must be reviewed immediately.
⚠ Critical Warning — Reactivation Window
"Iran's internet connectivity is recovering. As it normalizes, APT33, APT42, OilRig, and MuddyWater will regain full coordination capacity. Eclipse Intel assess a second, more sophisticated wave of state-sponsored operations is likely within days to weeks."
Defensive Priorities
Immediate Actions for Your Security Team
Elevate SOC posture to wartime footing immediately. 150+ incidents activated within 72 hours of the Feb 28 strikes. Ensure full SOC staffing including weekends and public holidays — many of these attacks targeted organizations during off-hours. Configure threat intelligence feeds to flag geopolitical escalation triggers and mandate escalation protocols for anomalous Middle East-related activity.
Activate and capacity-test DDoS mitigation now — before an incident. Banking, aviation, and logistics organizations are priority DDoS targets. DieNet and Keymous+ coordinate via Telegram with near-real-time targeting announcements, meaning attack onset can be extremely rapid. Defenses must be pre-activated. Verify mitigation is sized for high-volume volumetric attacks and test failover procedures this week.
Enforce phishing-resistant MFA across all accounts — SMS MFA is not sufficient. UK NCSC, Canadian Cyber Centre identify MFA as the single highest-impact defensive control in this threat environment. AI-enhanced phishing in this cycle is bypassing security awareness training. Move to FIDO2 hardware keys or app-based authenticators for all privileged, remote access, and high-value accounts.
Validate offline backups and test wiper recovery procedures. Handala and Moses Staff have both demonstrated wiper capability. Ensure backups are offline, offsite, and tested for end-to-end restoration. Protect Volume Shadow Copies from deletion. Mass file deletion events should trigger immediate SOC escalation. Run a recovery time drill against a wiper scenario this week — not after an incident.
Audit and diversify your Middle East cloud footprint immediately. The AWS UAE kinetic strike proves cloud infrastructure is now a physical military target. Audit all workloads in ME-CENTRAL-1 and ME-SOUTH-1. Implement m
Treat incoming ransomware as potential state-directed retaliation. Iran is routing retaliation through ransomware-as-proxy. If your organization has Middle East operations, Israeli business ties, Western government contracts, or critical infrastructure roles, apply nation-state incident response protocols — not standard criminal ransomware playbooks to any ransomware incident in the next 60 days.
Conduct emergency third-party and supply chain access review. Audit all vendor and third-party remote access. Enforce least privilege. Request emergency security attestations from critical suppliers. Pay particular attention to MSPs and software vendors with Middle East operations or Israeli product origins.
Brief at-risk employees on the RedAlert APK attack model and physical threat escalation. Staff in or traveling to the region must be warned against installing apps from unofficial sources, even if framed as emergency government alerts. For employees with Iranian diaspora backgrounds or vocal public profiles on the conflict, conduct a personal data security and physical security review given Handala's escalation to physical threat operations.
